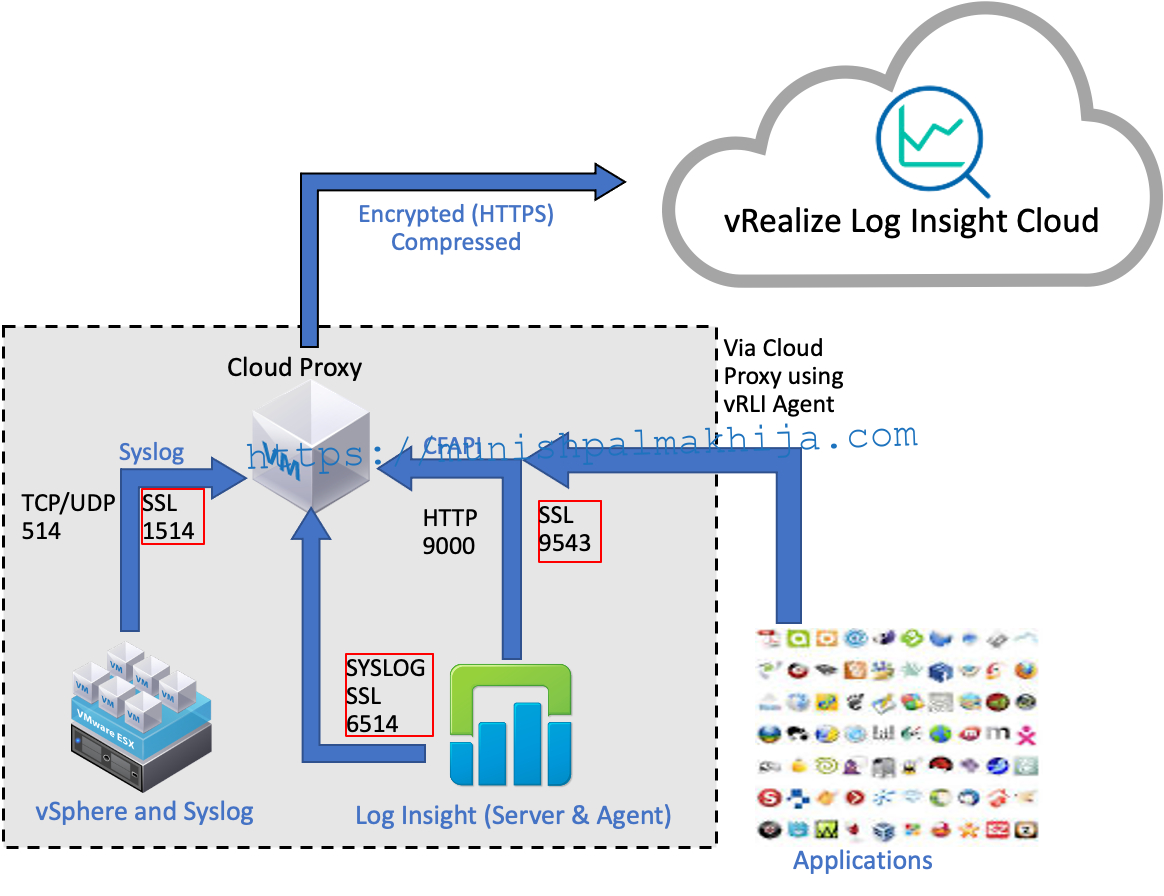
As part of the December release, vRealize Log Insight Cloud added SSL support for Cloud Proxy. You can now configure your log sources to forward logs over SSL to the Cloud Proxy.
In this blog, I will walk through the procedure to configure the SSL in li-agent and ESXi to securely send logs via cloud proxy to vRealize Log Insight Cloud.
- Configure SSL between the LI-Agents and Cloud Proxy.
- Configure SSL between the vSphere (ESXi Hosts) and Cloud Proxy.
My Lab Environment
- CentOS7 with li-agent 8.2
- vSphere 7 with nested ESXi server
Scenario 1 – Configure SSL between LI-Agents and Cloud Proxy
You can configure SSL between cloud proxy and li-agents
The Log Insight Agent stores certificates and uses them to verify the identity of the Cloud Proxy during all but the first connection to the Cloud Proxy. If the identity cannot be confirmed, the Log Insight Agent rejects the connection and writes an appropriate error message to the log. Certificates received by the agent are stored in the cert folder.
- For Windows, go to C:\ProgramData\VMware\Log Insight Agent\cert.
- For Linux, go to /var/lib/loginsight-agent/cert.
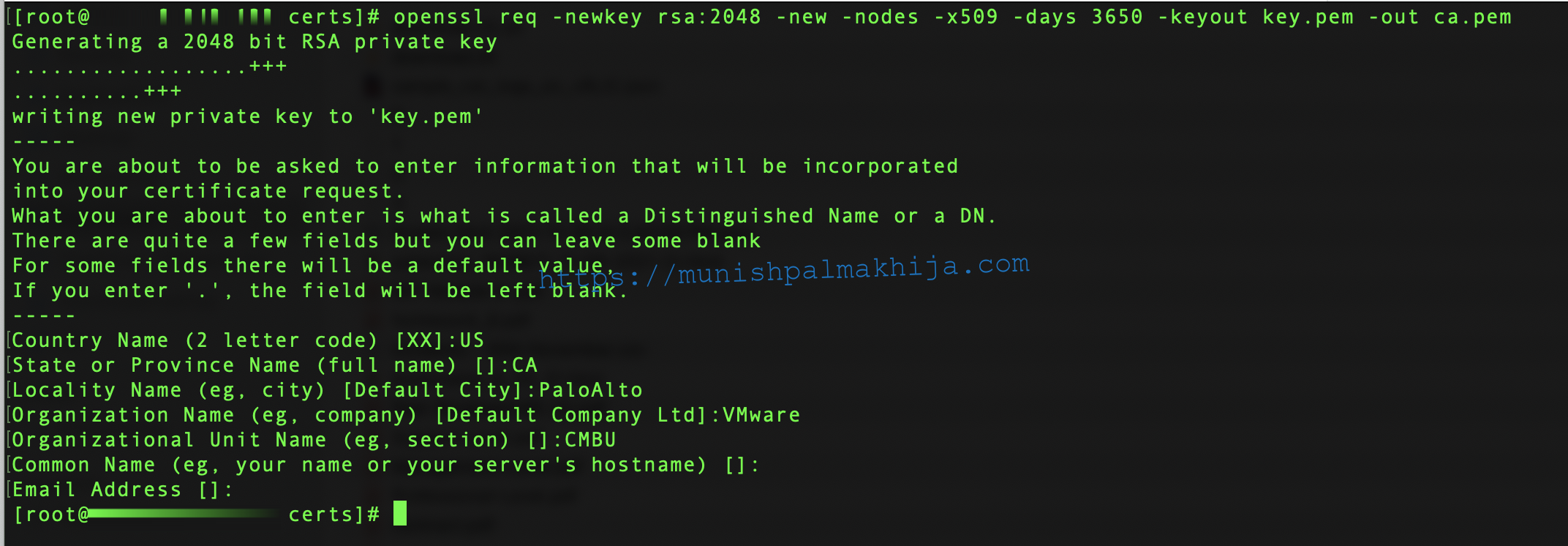
Step 1 – Generate a Self-Signed Certificate for an LI-Agent
You can generate a self-signed certificate for a vRealize Log Insight Windows or Linux agent by using the OpenSSL tool.
Prerequisites
If you don’t have it already, download the appropriate installer for OpenSSL from https://www.openssl.org/community/binaries.html.
Procedure
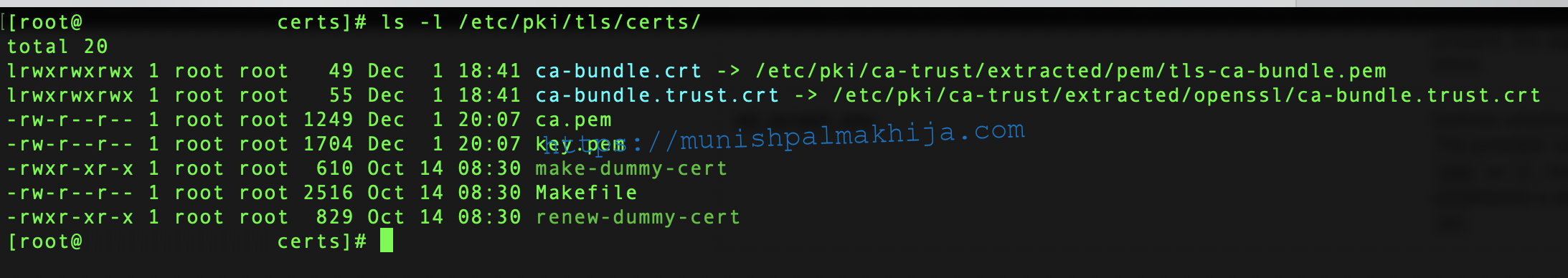
Create a certificate folder. In my case under the following path. The same needs to be specified in the liagent.ini file under ssl_ca_path
/etc/pki/tls/certs/
Open the Command Prompt and run the following command.
/etc/pki/tls/certs/ > openssl req -newkey rsa:2048 -new -nodes -x509 -days 3650 -keyout key.pem -out ca.pem
It will create 2 files
- key.pem is the private key.
- ca.pem is a certificate signed by key.pem
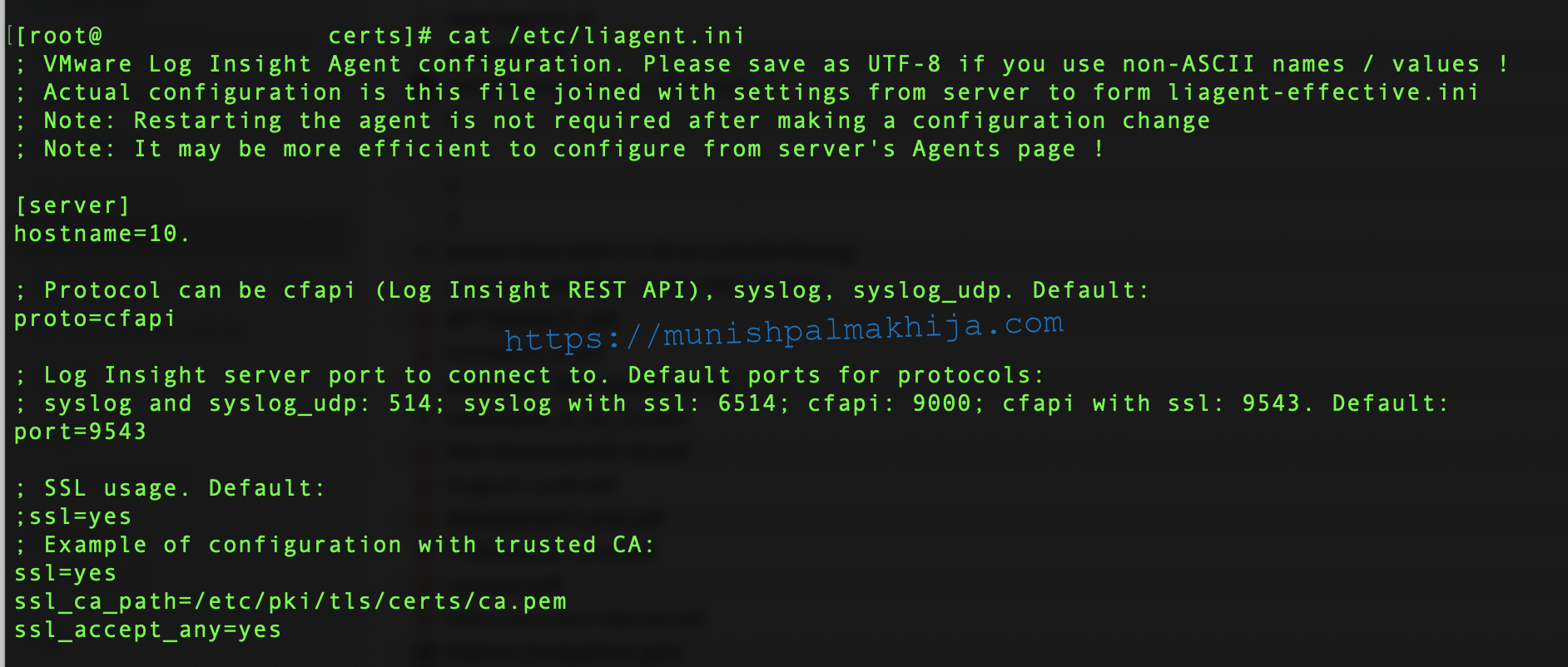
Step 2 – Configure SSL Parameters for an LI-Agent
Following is the procedure to configure SSL parameters on my centos machine
Prerequisites
- Cloud Proxy is reachable from VM where li-agent is installed.
- Ensure li-agent is installed and service is started
Procedure
Navigate to the folder containing the liagent.ini file and open in any editor.
- Linux /var/lib/loginsight-agent/
- Windows %ProgramData%\VMware\Log Insight Agent
My sample file for apache access logs
[server]
hostname=cloudproxy-ip
proto=cfapi
port=9543
ssl=yes
ssl_ca_path=/etc/pki/tls/certs/ca.pem
ssl_accept_any=yes
[filelog|apache-access]
directory=/var/log/httpd/
include = access
parser = apache-access
Note – For CA-signed certificate you can have ssl_accept_any=no & (name of the file in ssl_ca_path should match as given in the command above
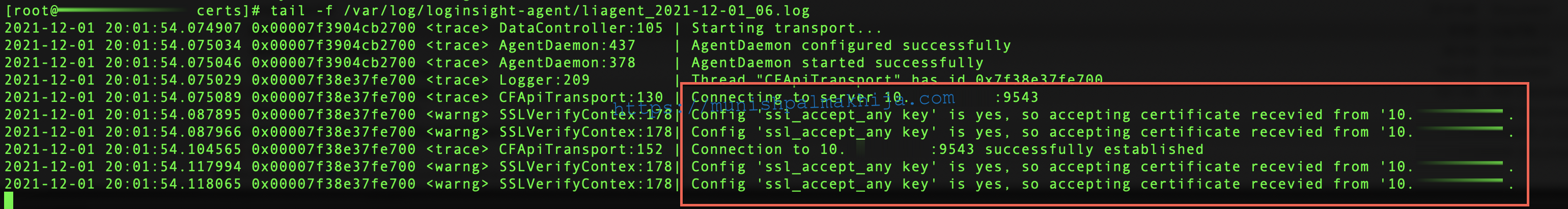
After you restart the li-agent service you should be able to verify li-agent logs to ensure connectivity is successfully established
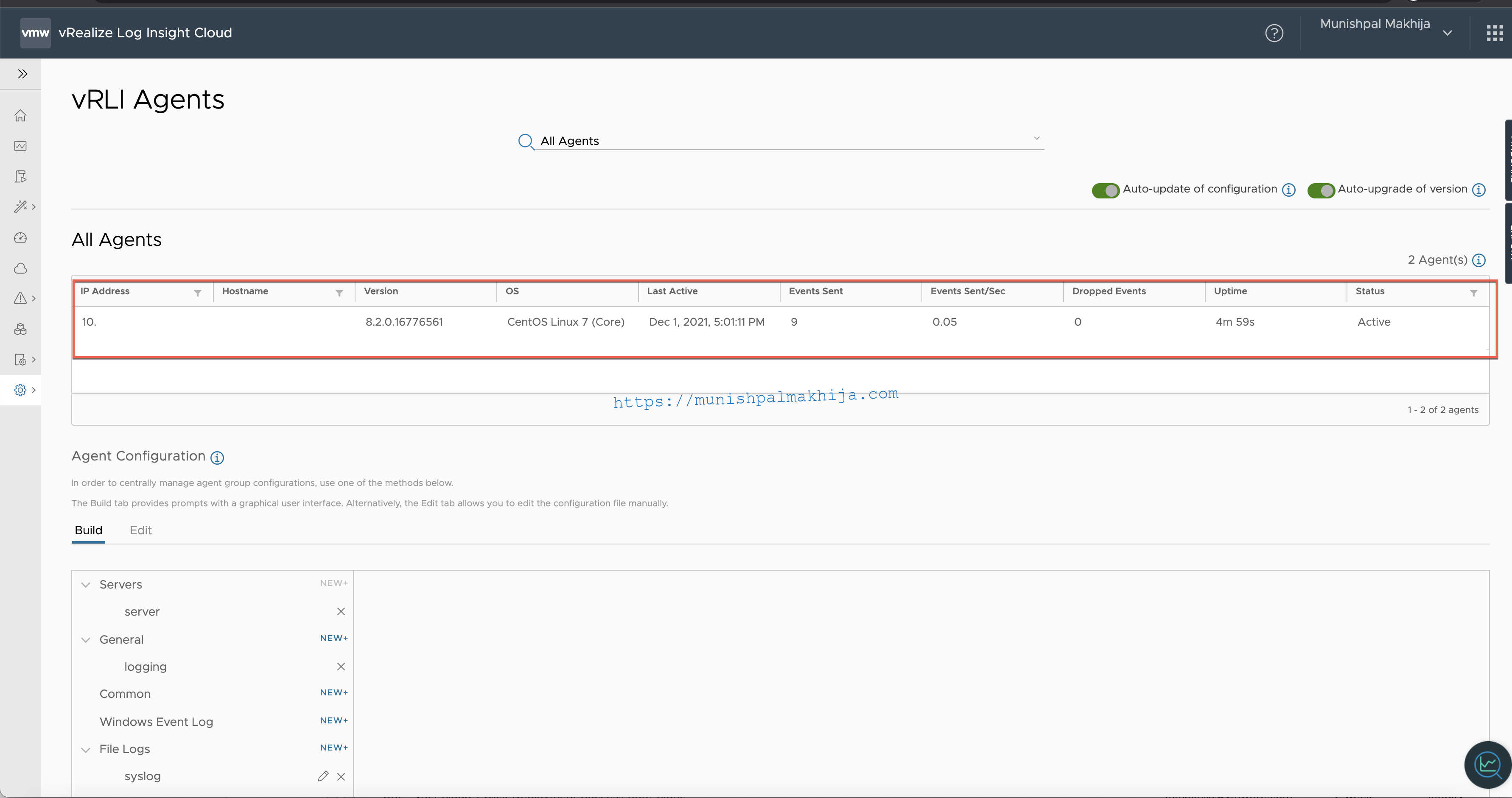
Verify if the li-agent is registered and logs are flowing
Navigate to vRLI Agents UI under Configuration
Scenario 2 – Configure SSL connection between vSphere (ESXi Hosts) and Cloud Proxy
Step 1 – Add a Log Forwarder Certificate to an ESXi Host Truststore
While configuring an ESXi host, if you select SSL as the protocol to forward log events to vRealize Log Insight Cloud, you have to manually add the log forwarder’s certificate to the ESXi host’s trust store.
Prerequisites
- Ensure Syslog is allowed in the ESXi Firewall under Configure –> System –> Firewall
- Cloud Proxy is reachable from ESXi Host(s).
Procedure
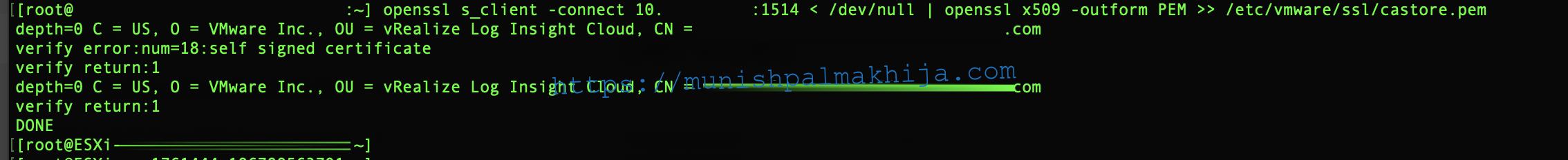
SSH to the ESXi host and execute following commands
openssl s_client -connect <CLOUD_PROXY_IP_HOSTNAME>:1514 < /dev/null | openssl x509 -outform PEM >> /etc/vmware/ssl/castore.pem
esxcli system syslog reload
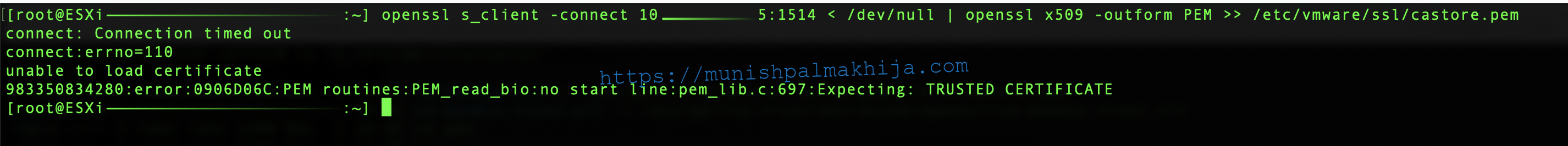
If the firewall is not configured you will see the following error
Step 2 – Connect vRealize Log Insight Cloud to a vSphere Environment
Following is the procedure how to connect vRealize Log Insight Cloud to a vSphere environment
Prerequisites
- Cloud Proxy is successfully deployed and reachable with resolvable fqdn.
- Verify and ensure you have appropriate privileges if using a service account instead of administrator@vsphere.local https://docs.vmware.com/en/VMware-vRealize-Log-Insight-Cloud/services/User-Guide/GUID-3F69731F-9D05-4E54-A26B-7FF80E4BA225.html
Procedure
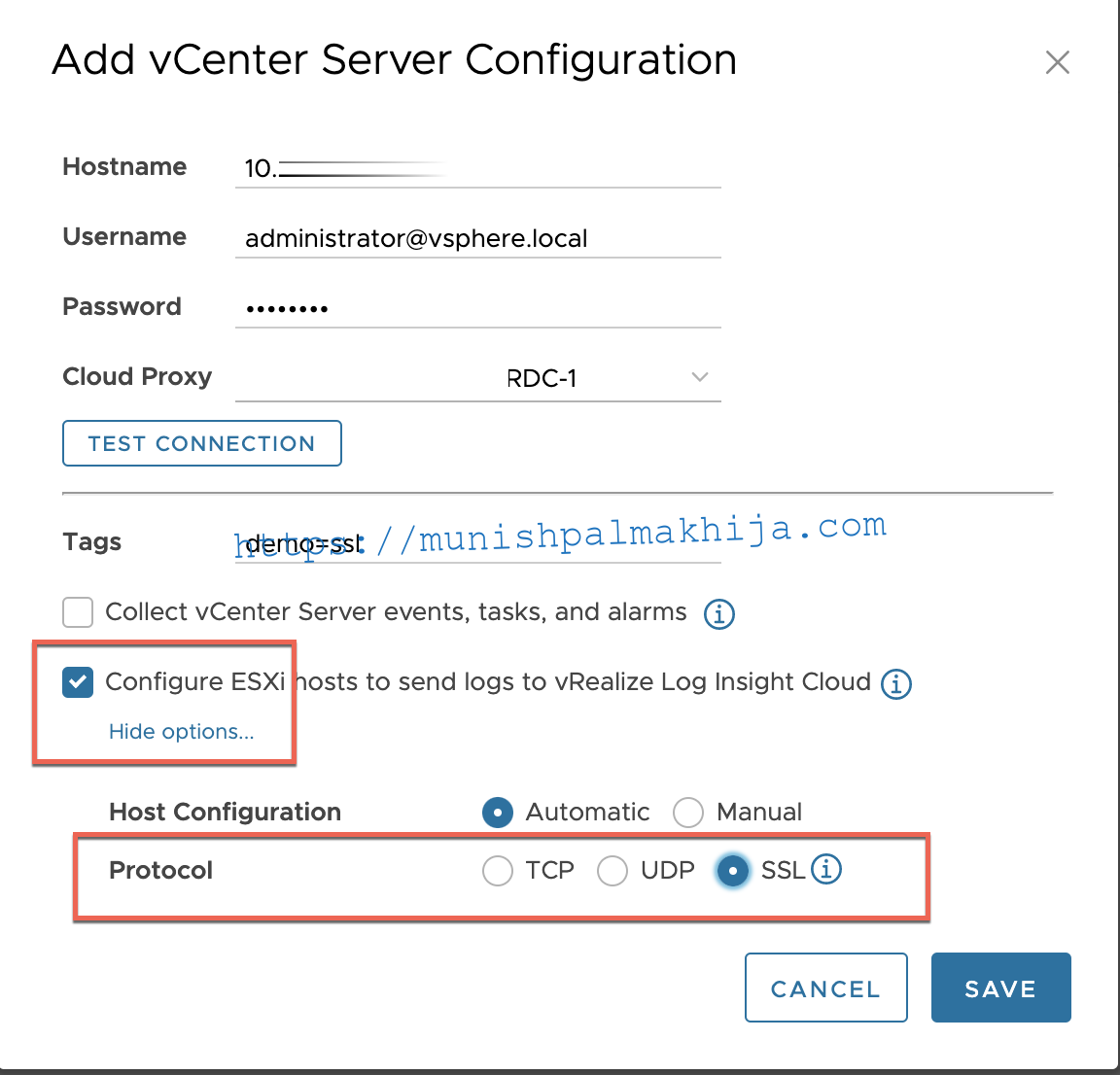
- Log in to vRealize Log Insight Cloud and navigate to Configuration > vSphere Integration.
- Click Add vCenter Server.
- In the Hostname text box, enter the IP address for the vCenter Server.
- Enter the credentials for the vCenter
- From the Cloud Proxy drop-down menu, select an installed Cloud Proxy.
- Select Configure ESXi hosts to send logs to vRealize Log Insight Cloud
- Under Advanced Options select SSL instead of TCP which is the default.
Once it is successfully saved you can verify if the ESXi has SSL configure
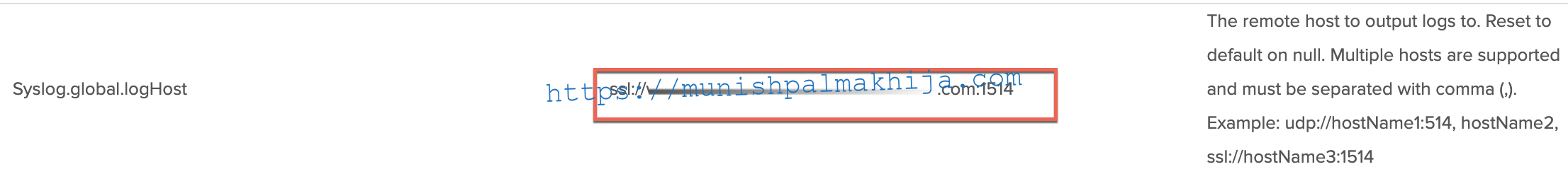
Next, you can verify on the ESXi host if the Syslog.global.loghost has proper SSL configuration
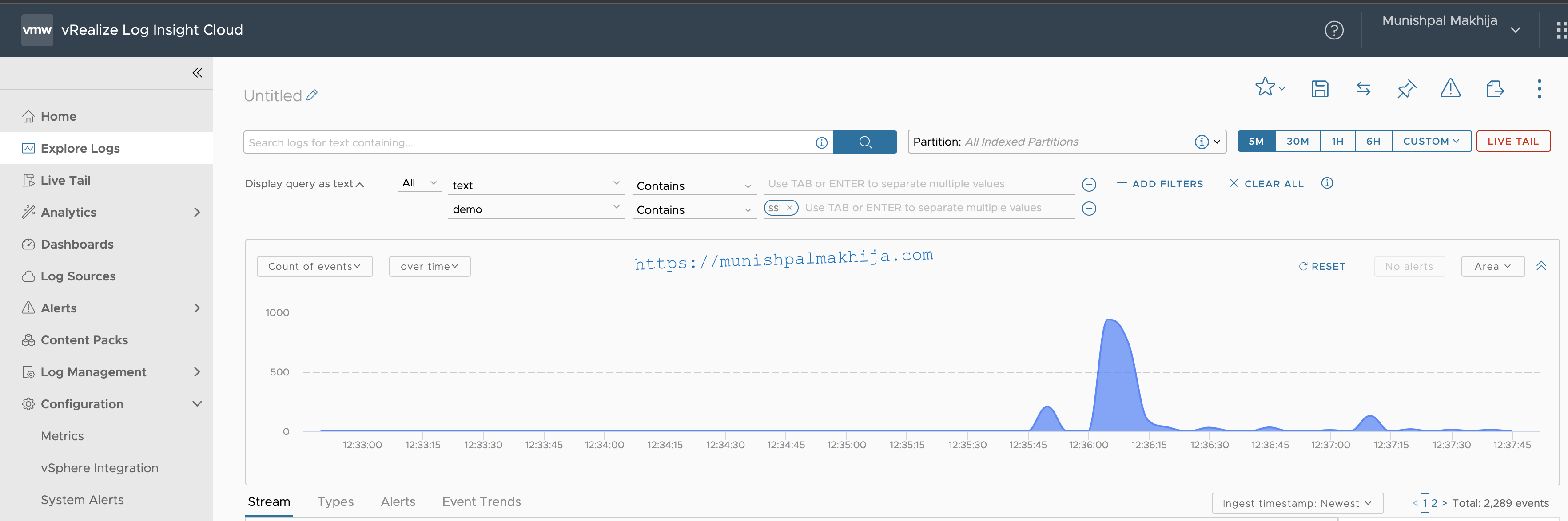
Verify Logs
Related Articles